We Protect the World's
Most Sensitive API Data Using Generative
AI
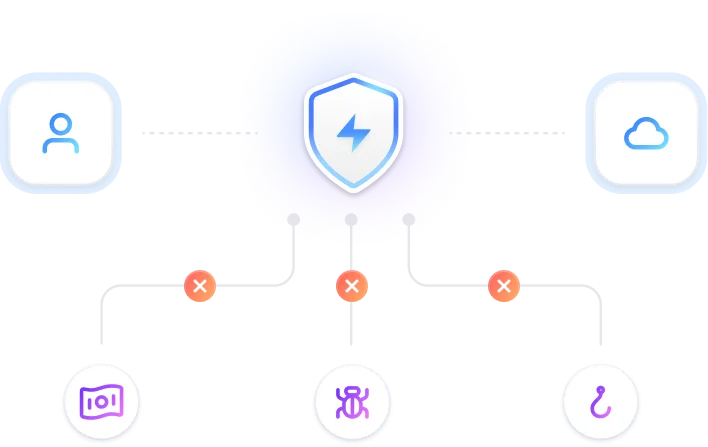
In today’s rapidly changing threat environment, maintaining robust cybersecurity is a significant challenge for organisations. Traditional methods typically focus on reactive measures, allocating resources to defend against the most prominent known threats. The Generative AI API Security Scanning, provided by APISecurityEngine, revolutionises this approach by proactively scanning APIs to identify and mitigate potential security risks before they can be exploited
Recognized by Global Standards





5 threats found

About Us
We Offer Professional
API Security Solutions
Only platform which provides full security coverage of your API’s in a single dashboard with agentless solutions and helps to reduce the attack surface through continuous monitoring with zero manual efforts.
Our Product
Proactive API Security Monitoring Engine
Reduced attack surface of APIs and increased security convergence implemented for customer demands to improve cyber resilience
Proactive Automated API Security
Our API security solutions are designed to provide end-to-end protection for APIs, including authentication and threat detection and prevention.

API Security Monitoring
Continuous monitoring of data security in API attacks is essential to detect and mitigate these risks in a timely manner.



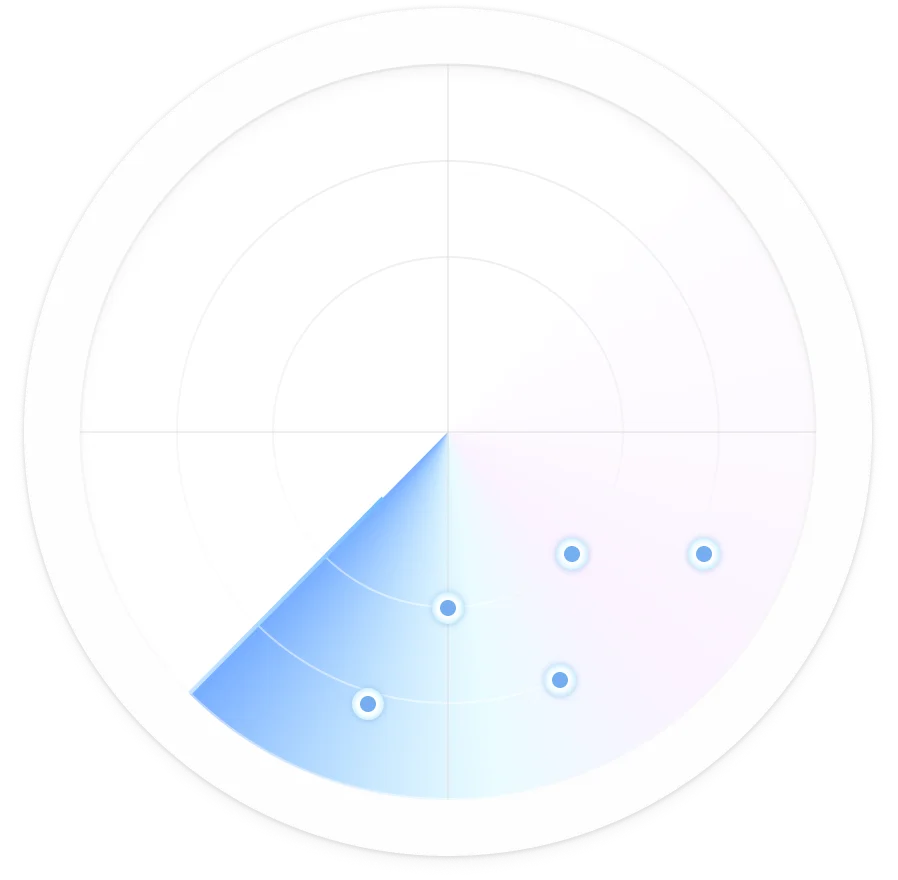
Utilise Your Breach Assessment Score
APISecurityEngine is an advanced tool designed to enhance the security of APIs by leveraging the power of Generative AI.
Solutions for every security goal
APISecurityEngine scalable solutions adapt to your needs, ensuring robust protection without compromise.
API Security Monitoring
Continuous monitoring of data security in API attacks is essential to detect and mitigate these risks in a timely manner.
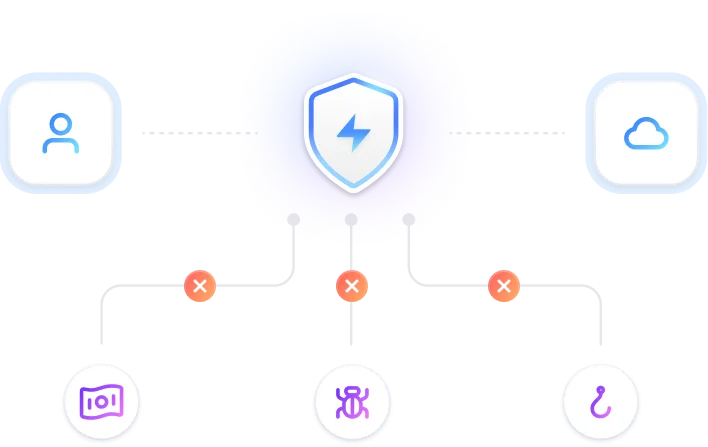
Threat Model Your API’s
Empower your API security with APISecurityEngine, a cutting-edge tool designed to leverage generative AI for comprehensive threat modelling and attack surface monitoring.
Utilise Your Breach Assessment Score
APISecurityEngine is an advanced tool designed to enhance the security of APIs by leveraging the power of Generative AI.
API Security
Secure your business with our Security Engine
Only platform which provides full security coverage of your API’s in a single dashboard with agentless solutions and helps to reduce the attack surface through continuous monitoring with zero manual efforts.